![[FORECASTS] From Password Sprays to Tenant Sabotage: The 8-Week Iran Cyber Risk for U.S. and Israeli Orgs - UPDATED: 2026-03-26](/content/images/size/w600/2026/03/z-6.png)
[FORECASTS] From Password Sprays to Tenant Sabotage: The 8-Week Iran Cyber Risk for U.S. and Israeli Orgs - UPDATED: 2026-03-26
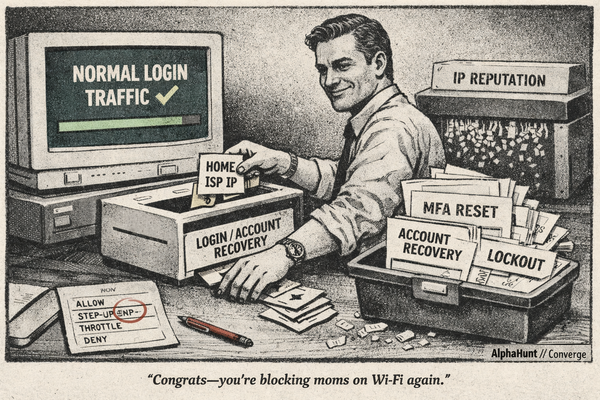
Iran cyber risk is not about whether they’ll be active. They will. The real question is whether the next 8 weeks produce a publicly attributed, materially disruptive hit with a new twist beyond the usual password-spray sludge. Tenant sabotage is the part to watch. 👀🔥

![[SIGNALS WEEKLY] Ransomware’s New Priority Targets—Hypervisors, Recovery Paths, and Control Planes](/content/images/size/w600/2026/03/z-5.png)
![[FORECAST] Will RedNovember be publicly reported to exploit at least one zero-day vulnerability in 2026? Updated 2026-03-24](/content/images/size/w600/2026/03/z-4.png)
![[DEEP RESEARCH] How Malware Uses Solana and EVM Chains to Rotate C2 Without Burning Infrastructure](/content/images/size/w600/2026/03/z-3.png)
![[SIGNALS WEEKLY] GitHub, npm, and Fake Interviews: Why Developer Supply Chain Attacks Are Converging](/content/images/size/w600/2026/03/zz-3.png)
![[FORECASTS] From Password Sprays to Tenant Sabotage: The 8-Week Iran Cyber Risk for U.S. and Israeli Orgs](/content/images/size/w600/2026/03/z-2.png)
![[FORECAST UPDATED] After LockBit and BlackCat, Is Cl0p Really Next in Line?](/content/images/size/w600/2026/03/zz-1.png)

![[DEEP RESEARCH] When Gambling Becomes a Money-Transfer Rail](/content/images/size/w600/2026/03/z-1.png)
![[DEEP RESEARCH] Who’s Most Likely to Abuse MCP Integrations? UNC3944, TraderTraitor, UNC6293](/content/images/size/w600/2026/03/z.png)
![[FORECAST UPDATED] AI Agents as Regulated C2: Will Anyone Be Forced to Act?](/content/images/size/w600/2026/02/z-11.png)
![[FORECAST] Fortune 500s: Will Prompt Injection Trick IDE Agent Mode into Running Commands—or Leaking Secrets—by 2026?](/content/images/size/w600/2026/02/z-10.png)


![[FORECAST] Dismantled or Displaced? Cambodia’s Scam-Compound Crackdown by 2030?](/content/images/size/w600/2026/02/z-7.png)

![[DEEP RESEARCH] BadIIS Isn’t Enough: The IIS Module + HTTP Fingerprints That Catch SEO-Fraud Cloaking](/content/images/size/w600/2026/02/z-2.png)
![[FORECAST] ShinyHunters SaaS Data Theft: Why Non-Ransom Monetization Looks Increasingly Attractive](/content/images/size/w600/2026/02/z.png)