cl0p
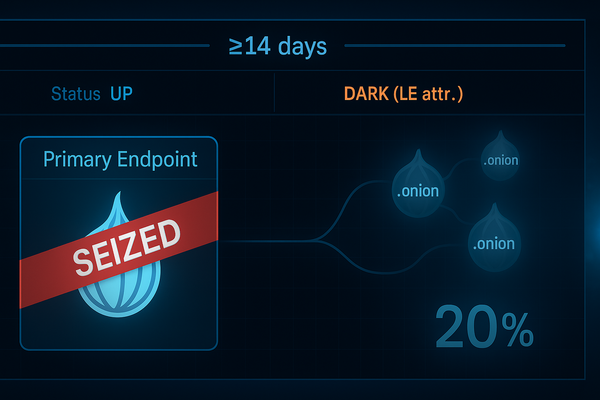
Cl0p’s Leak Sites: 20% Chance They Go Dark by Apr 22, 2026
Forecast: 20% chance Cl0p’s leak sites go dark by Apr 22, 2026. Needs a seizure banner or ≥14 days down w/ LE attribution. Cronos showed it’s doable; mirrors make it brutal.
cl0p
Forecast: 20% chance Cl0p’s leak sites go dark by Apr 22, 2026. Needs a seizure banner or ≥14 days down w/ LE attribution. Cronos showed it’s doable; mirrors make it brutal.

weekly
SNMP rootkits on Cisco (CVE-2025-20352) 🎛️, F5 source-code heist + CISA ED 26-01 🚨, and 175 MS CVEs 📅. Pick your poison: harden SNMP or inventory+patch BIG-IP today.
storm-2603
Workday was the first stop, not the destination. We’re at 62% odds it hits another payroll stack by 2026-04-17. Harden all the paydoors, not just the pretty one.

cl0p
Oracle EBS got in-memory Java loaders, not lockerware. Patch CVE-2025-61882, lock egress, hunt TemplatePreviewPG with TMP|DEF + XSL-TEXT|XML. Extortion rides in via “pubstorm.”

ta558
Which scenario will best describe TA558’s (aka RevengeHotels) evolution by June 30, 2026?
forecasts
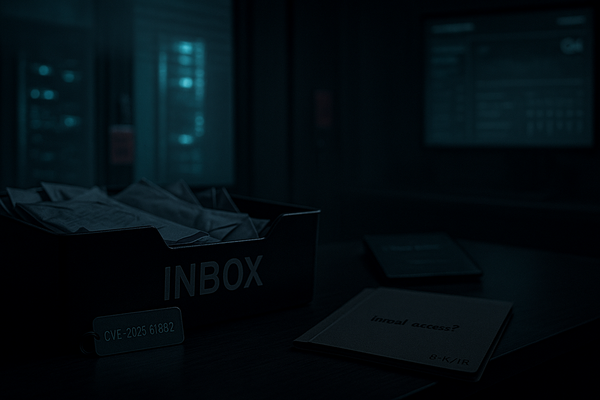
Oracle EBS zero-day (CVE-2025-61882): OOB patch, KEV-listed, exec extortion emails flying. We’re at 76% that a primary source names it as initial access by 12/31. Raise or fade? 🧨🧭

china
RedNovember likely stays fast-follow on edge devices using N-days and public PoCs, not 0-days. China-nexus peers show willingness to burn edge 0-days, so a pivot is plausible but not base case...

unc5221
Question: By Dec 31, 2025, will UNC5221 be publicly linked to exploiting at least one new zero-day in a non-Ivanti edge platform (e.g., VMware vCenter/ESXi, Citrix NetScaler, F5, Palo Alto, Fortinet)?

void-proxy
VoidProxy is reshaping the phishing landscape, enabling adversaries to bypass MFA and hijack enterprise cloud sessions with minimal technical skill. Its rapid adoption, use of trusted email providers, and evasive infrastructure demand urgent, layered defenses—especially for organizations...

c2
Attackers are rapidly shifting to modular, cloud-integrated C2 frameworks—Sliver, Havoc, Mythic, Brute Ratel C4, and Cobalt Strike—blurring lines between APT and cybercrime. These tools’ stealth, automation, and cloud API abuse are outpacing legacy detection, demanding urgent defensive adaptation.

geopolitics
Financial institutions are quietly overhauling cyber defenses, blending geopolitical risk with threat intelligence to counter state-sponsored attacks and regulatory pressure. This shift is driving new investments in automation, incident response, and sector-wide collaboration..

ta558
TA558’s “SteganoAmor” campaign leverages steganography to deliver commodity malware across oil, gas, maritime, and industrial targets. The group’s use of image-embedded payloads and compromised infrastructure...