SIGNALS WEEKLY: When Trust Breaks- Pipelines, PLM, and Phishing at Scale
Everyone loves “shift left” until the thing in the pipeline shifts your secrets somewhere else. Security tooling has officially joined the attack surface like it was invited.
TL;DR
- [Supply Chain/CI-CD] The Trivy compromise remains a multi-stage supply chain campaign (upstream tampering → credential theft → follow-on cloud/repo abuse), with CISA KEV inclusion of CVE-2026-33634 signaling ongoing exploitation risk and prioritizing rapid mitigation and secret rotation.
- [Vulnerabilities/OT] CISA issued an ICS advisory for a CVSS 10 unsafe-deserialization RCE affecting PTC Windchill PDMLink/FlexPLM (CVE-2026-4681); with a vendor fix pending, near-term risk reduction centers on immediate web-tier workaround controls for exposed deployments.
- [Geopolitics/Phishing] Iran-linked activity shows an infrastructure surge—thousands of conflict-themed phishing URLs across thousands of hostnames and broad brand impersonation—supporting sustained credential-theft/fraud operations and elevating disruptive-risk concerns (including wiper scenarios).
AlphaHunt
Stop doomscrolling, start decisioning. We chewed through the muck so your team doesn’t have to. → Subscribe!
Like this? Forward this to a friend!
(Have feedback? Did something resonate with you? Did something annoy you? Just hit reply! :))
Current Stories
TL;DR
-
[Supply Chain/CI-CD] Trivy’s compromise continues to play out as an end-to-end campaign (upstream tampering → credential harvest → follow-on cloud/repo abuse); CISA added CVE-2026-33634 to KEV, reinforcing patch/rotate urgency for affected pipelines.
-
[Vulnerabilities/OT] CISA warned of critical (CVSS 10) RCE via unsafe deserialization in PTC Windchill PDMLink/FlexPLM (CVE-2026-4681); PTC is developing a fix, but CISA highlights immediate Apache/IIS workaround steps—especially for internet-accessible deployments.
-
[Geopolitics] Unit 42’s Iran-linked update adds concrete scale and tradecraft: 7,381 conflict-themed phishing URLs across 1,881 hostnames, plus enterprise/consumer impersonation at pace (telecoms, airlines, law enforcement, energy) and elevated wiper risk; defenders should treat this as an active infrastructure surge, not ambient tension.
References
-
(2026-03-26) CISA Adds One Known Exploited Vulnerability to Catalog
-
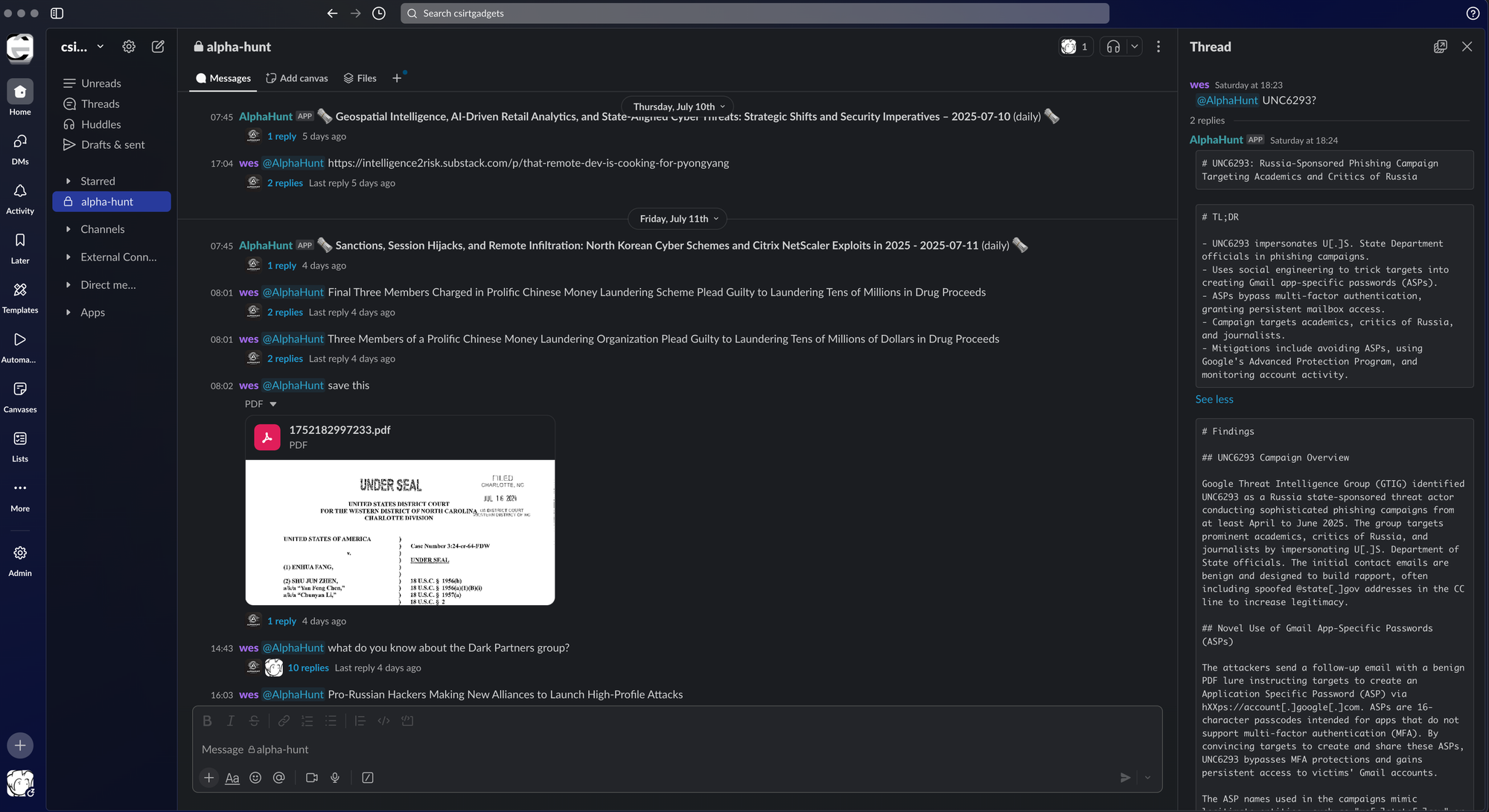
(2026-03-24) Guidance for detecting, investigating, and defending against the Trivy supply chain compromise
-
(2026-03-25) Update: Ongoing Investigation and Continued Remediation
-
(2026-03-30) Tracking TeamPCP: Investigating Post-Compromise Attacks Seen in the Wild
-
(2026-03-26) PTC Windchill Product Lifecycle Management
-
(2026-03-26) Threat Brief: March 2026 Escalation of Cyber Risk Related to Iran (Updated March 26)
AlphaHunt Converge - Plug in your Flight Crew
Get intelligence where it counts. No dashboards. No detours. AlphaHunt Converge teases out your intent, reviews the results and delivers actionable intel right inside Slack. We turn noise into signal and analysts into force multipliers.
Anticipate, Don’t Chase.


![[FORECASTS] From Password Sprays to Tenant Sabotage: The 8-Week Iran Cyber Risk for U.S. and Israeli Orgs - UPDATED: 2026-03-26](/content/images/size/w600/2026/03/z-6.png)
![[SIGNALS WEEKLY] Ransomware’s New Priority Targets—Hypervisors, Recovery Paths, and Control Planes](/content/images/size/w600/2026/03/z-5.png)
![[FORECAST] Will RedNovember be publicly reported to exploit at least one zero-day vulnerability in 2026? Updated 2026-03-24](/content/images/size/w600/2026/03/z-4.png)