SIGNALS WEEKLY: How AI Is Turbocharging Attacks on 600+ FortiGate Firewalls
Your firewall isn’t the perimeter. It’s the onboarding portal. 🔥

TL;DR
- [Vulnerabilities] Active, multi-actor exploitation of internet-exposed management planes (Dell RecoverPoint for VMs, BeyondTrust Remote Support/Privileged Remote Access, Ivanti EPMM) is yielding pre-auth RCE, webshell deployment, and rapid pivots into VMware, AD, and backups; patching must be paired with compromise assessment to find startup-script and webroot persistence.
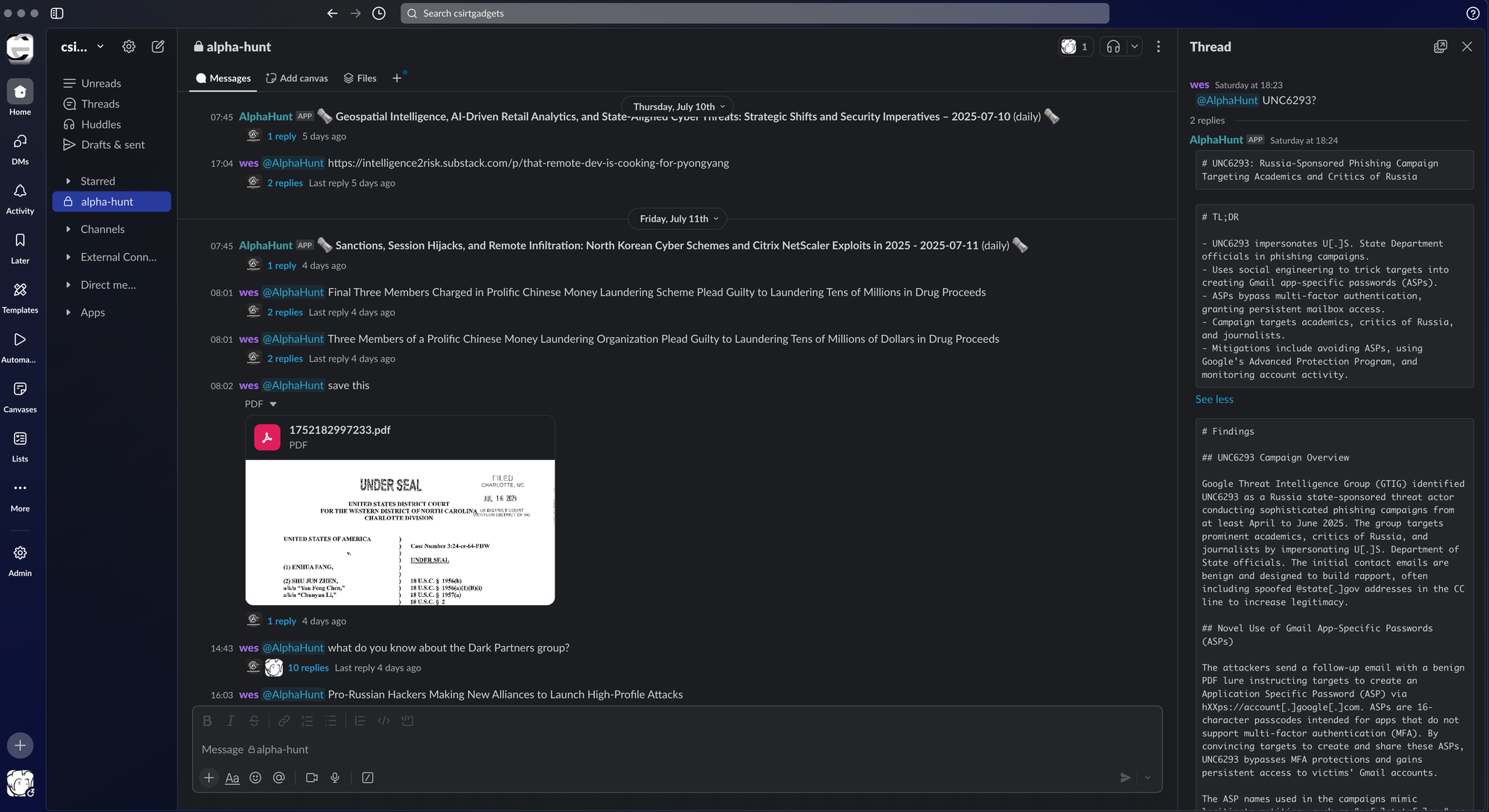
- [Threat Actors] Both state-linked and financially motivated actors are industrializing edge compromise: UNC6201 (likely PRC) weaponizing Dell RecoverPoint zero-day with Tomcat WAR + custom webshells, while Russian-speaking criminals leverage commercial genAI to script and scale exploitation of 600+ FortiGate devices for configuration/credential theft and deeper access.
- [OT/Cloud/Geopolitics] OT intrusions and Russian operations against Ukraine’s energy sector are shifting from immediate disruption to control-loop and infrastructure mapping to support kinetic targeting; in parallel, cloud intrusions increasingly rely on misconfigurations, credential abuse, and native APIs (snapshots, backups, keys) for “cloud ransomware” and destructive actions that look like legitimate admin activity.
AlphaHunt
Stop doomscrolling, start decisioning. We chewed through the muck so your team doesn’t have to. → Subscribe!
Like this? Forward this to a friend!
(Have feedback? Did something resonate with you? Did something annoy you? Just hit reply! :))
Current Stories
TL;DR
-
[Vulnerabilities] Edge/remote-access exploitation wave: multiple internet-exposed management planes are being hit with pre-auth RCE / default-credential paths, followed by webshelling and fast pivots into identity/virtualization.
-
Dell RecoverPoint for VMs (CVE-2026-22769, CVSS 10.0): UNC6201 (suspected PRC-nexus) exploited since at least mid-2024; Tomcat Manager WAR deployment + SLAYSTYLE webshell, persistence via boot-time script modification, and VMware pivoting (e.g., “Ghost NICs”, iptables SPA).
-
BeyondTrust Remote Support / Privileged Remote Access (CVE-2026-1731): active exploitation observed with post-exploitation including account creation, webshells, data theft, and RATs (e.g., VShell, SparkRAT).
-
Ivanti EPMM (CVE-2026-1281 / CVE-2026-1340): two zero-days under widespread exploitation; activity includes reverse shells, JSP webshell writes, recon, and attempts to establish durable access.
-
-
[Geopolitics] Ukraine reports Russian cyber operations against energy networks increasingly used for targeting intelligence (facility mapping, repair tracking, damage assessment) to support missile strikes, rather than immediate disruption.
-
[Vulnerabilities] CISA added two actively exploited Roundcube Webmail issues (CVE-2025-49113, CVE-2025-68461) to KEV, signaling renewed webmail targeting and urgent patch prioritization.
References
-
(2026-02-17) From BRICKSTORM to GRIMBOLT: UNC6201 Exploiting a Dell RecoverPoint for Virtual Machines Zero-Day
-
(2026-02-19) VShell and SparkRAT Observed in Exploitation of BeyondTrust Critical Vulnerability (CVE-2026-1731)
-
(2026-02-17) Critical Vulnerabilities in Ivanti EPMM Exploited
-
(2026-02-23) Ukraine says cyberattacks on energy grid now used to guide missile strikes
-
(2026-02-20) CISA Adds Two Known Exploited Vulnerabilities to Catalog
AlphaHunt Converge - Plug in your Flight Crew
Get intelligence where it counts. No dashboards. No detours. AlphaHunt Converge teases out your intent, reviews the results and delivers actionable intel right inside Slack. We turn noise into signal and analysts into force multipliers.
Anticipate, Don’t Chase.


![[DEEP RESEARCH] TeamPCP’s CI/CD Trust Inversion: When “Pinned” Actions Become Initial Access](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/04/z-1.png)