[SIGNALS WEEKLY] GitHub, npm, and Fake Interviews: Why Developer Supply Chain Attacks Are Converging
2026 cyber lesson: attackers don’t need your prod box first. They want your dev, your repo, your package manager, and your CI runner. Force-pushes, fake interviews, poisoned installers. Real classy stuff. 🤡🔧🔥
![[SIGNALS WEEKLY] GitHub, npm, and Fake Interviews: Why Developer Supply Chain Attacks Are Converging](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w1200/2026/03/zz-3.png)
TL;DR
-
[Supply Chain] Adversaries are systematically compromising GitHub accounts and npm packages, using force-pushes and install hooks plus Solana-based dead-drop C2 to spread Python/JavaScript malware at scale.
-
[Developer Targeting] Developer-focused social engineering (fake interviews, SEO-poisoned tools, hijacked orgs) is now a primary path to secrets, wallets, and CI credentials.
-
[Vulnerabilities] Actively exploited automation/file-transfer flaws (n8n, Wing FTP) and emerging prompt abuse in AI tools expand the attack surface beyond traditional malware-centric models.
AlphaHunt
Stop doomscrolling, start decisioning. We chewed through the muck so your team doesn’t have to. → Subscribe!
Like this? Forward this to a friend!
(Have feedback? Did something resonate with you? Did something annoy you? Just hit reply! :))
Current Stories
TL;DR
-
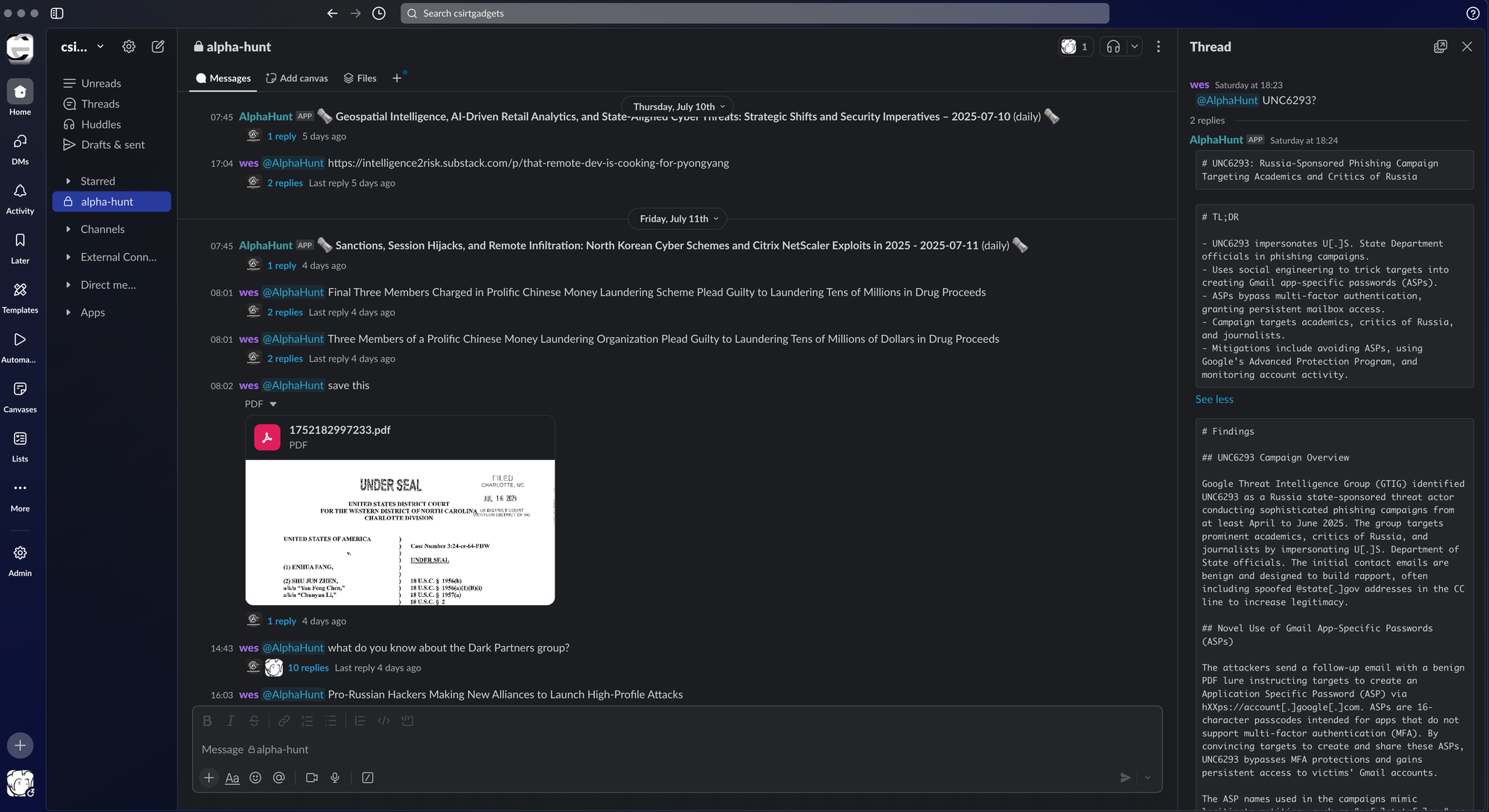
[Supply Chain] ForceMemo: StepSecurity reported a large-scale GitHub account takeover and force-push campaign that injected obfuscated Python malware into hundreds of repos and used Solana as a dead-drop C2 channel.
-
[Developer Targeting] Microsoft reported the Contagious Interview campaign targeting developers via fake recruiting workflows, using malicious code and editor trust prompts to deploy backdoors and steal secrets.
-
[Threat Actors] Microsoft reported Storm-2561 using SEO poisoning to distribute trojanized, digitally signed fake VPN installers that harvest credentials.
-
[Vulnerabilities] CISA added actively exploited issues to the KEV catalog, including CVE-2025-68613 affecting n8n and CVE-2025-47813 affecting Wing FTP Server, increasing urgency for patching internet-facing automation and file-transfer services.
-
[Law Enforcement] INTERPOL Operation Synergia III reported disruption of 45,000 malicious IPs and servers and 94 arrests, reflecting continued multinational pressure on criminal infrastructure.
References
-
(2026-03-14) ForceMemo: Hundreds of GitHub Python Repos Compromised via Account Takeover and Force-Push - StepSecurity
-
(2026-03-11) Contagious Interview: Malware delivered through fake developer job interviews | Microsoft Security Blog
-
(2026-03-12) Storm-2561 uses SEO poisoning to distribute fake VPN clients for credential theft | Microsoft Security Blog
-
(2026-03-11) CISA Adds One Known Exploited Vulnerability to Catalog | CISA
-
(2026-03-16) CISA Adds One Known Exploited Vulnerability to Catalog | CISA
-
(2026-03-13) 45,000 malicious IP addresses taken down in international cyber operation
AlphaHunt Converge - Plug in your Flight Crew
Get intelligence where it counts. No dashboards. No detours. AlphaHunt Converge teases out your intent, reviews the results and delivers actionable intel right inside Slack. We turn noise into signal and analysts into force multipliers.
Anticipate, Don’t Chase.


![[DEEP RESEARCH] TeamPCP’s CI/CD Trust Inversion: When “Pinned” Actions Become Initial Access](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/04/z-1.png)