[SIGNALS WEEKLY] Converging Control-Plane Threats Across Modern Infrastructure
Everyone loves “endpoint visibility” until the incident starts in the control plane they treated like support infrastructure. Routers, CI/CD, token flows, web admin panels — same neglect, better attacker ROI.
![[SIGNALS WEEKLY] Converging Control-Plane Threats Across Modern Infrastructure](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w1200/2026/04/z-2.png)
TL;DR
-
[Control Planes] Adversaries increasingly target under-monitored control layers—OT gateways, SOHO routers, vCenter, CI/CD, and DNS—for scalable, stealthy access that bypasses traditional endpoint-focused defenses.
-
[Identity & Tokens] AI-enabled phishing and device-code abuse are accelerating token theft and OAuth/session persistence, making legitimate-looking identity flows the primary long-term foothold over malware-on-endpoint.
-
[Supply Chain & Ransomware] Malicious package updates and rapid N‑day exploitation of internet-facing apps are turning developer tooling and perimeter services into high-yield entry points for espionage, data theft, and fast-moving ransomware.
AlphaHunt
Stop doomscrolling, start decisioning. We chewed through the muck so your team doesn’t have to. → Subscribe!
Like this? Forward this to a friend!
(Have feedback? Did something resonate with you? Did something annoy you? Just hit reply! :))
Current Stories
TL;DR
-
[OT / Critical Infrastructure] Iran-affiliated actors are exploiting internet-exposed PLC environments to disrupt operations; expect localized outages/process disruption risk for operators with externally reachable OT.
-
[Cyber Espionage / Edge Devices] Russian-linked activity is leveraging mass SOHO-router compromise to hijack DNS and enable adversary-in-the-middle access; remote users/branches are the most likely initial impact zone.
-
[Supply Chain / North Korea] A malicious npm Axios release delivered RAT payloads via dependency hijacking; developer workstations and CI/CD are at elevated risk of secret theft and downstream cloud compromise.
-
[Ransomware] Medusa operators are accelerating exploitation of newly disclosed web-facing flaws for rapid ransomware deployment; patch-lagged perimeter apps remain the highest-probability entry point.
-
[Vulnerabilities / Active Exploitation] CISA added CVE-2026-35616 (Fortinet FortiClient EMS) to KEV due to active exploitation; endpoint-management infrastructure should be treated as Tier-0 exposure.
AlphaHunt Converge - Plug in your Flight Crew
Get intelligence where it counts. No dashboards. No detours. AlphaHunt Converge teases out your intent, reviews the results and delivers actionable intel right inside Slack. We turn noise into signal and analysts into force multipliers.
Anticipate, Don’t Chase.
References
-
(2026-04-07) Iranian-Affiliated Cyber Actors Exploit Programmable Logic Controllers Across US Critical Infrastructure
-
(2026-04-07) SOHO router compromise leads to DNS hijacking and adversary-in-the-middle attacks
-
(2026-04-01) Mitigating the Axios npm supply chain compromise
-
(2026-04-06) Storm-1175 focuses gaze on vulnerable web-facing assets in high-tempo Medusa ransomware operations
-
(2026-04-06) CISA Adds One Known Exploited Vulnerability to Catalog


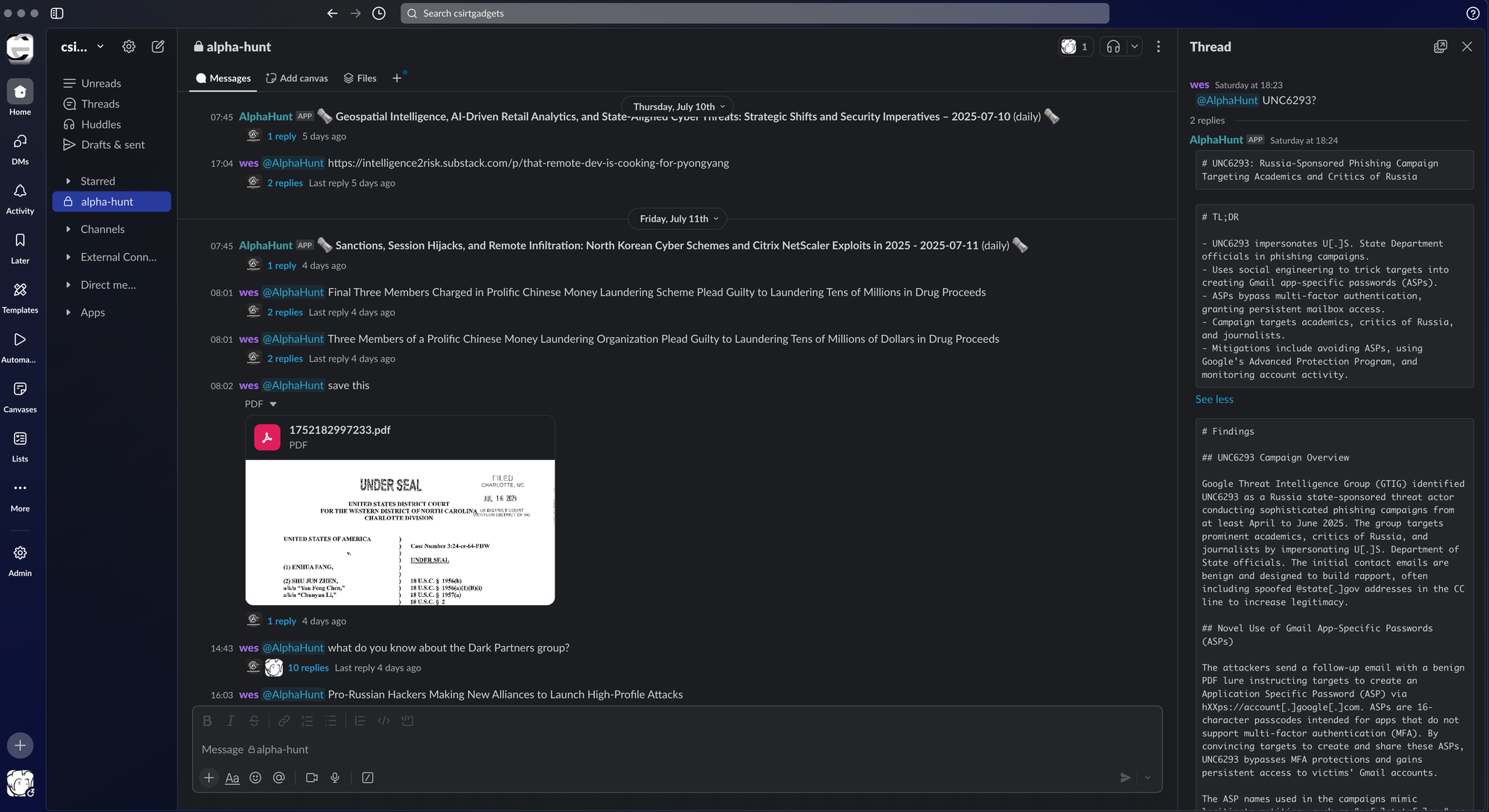
![[DEEP RESEARCH] TeamPCP’s CI/CD Trust Inversion: When “Pinned” Actions Become Initial Access](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/04/z-1.png)