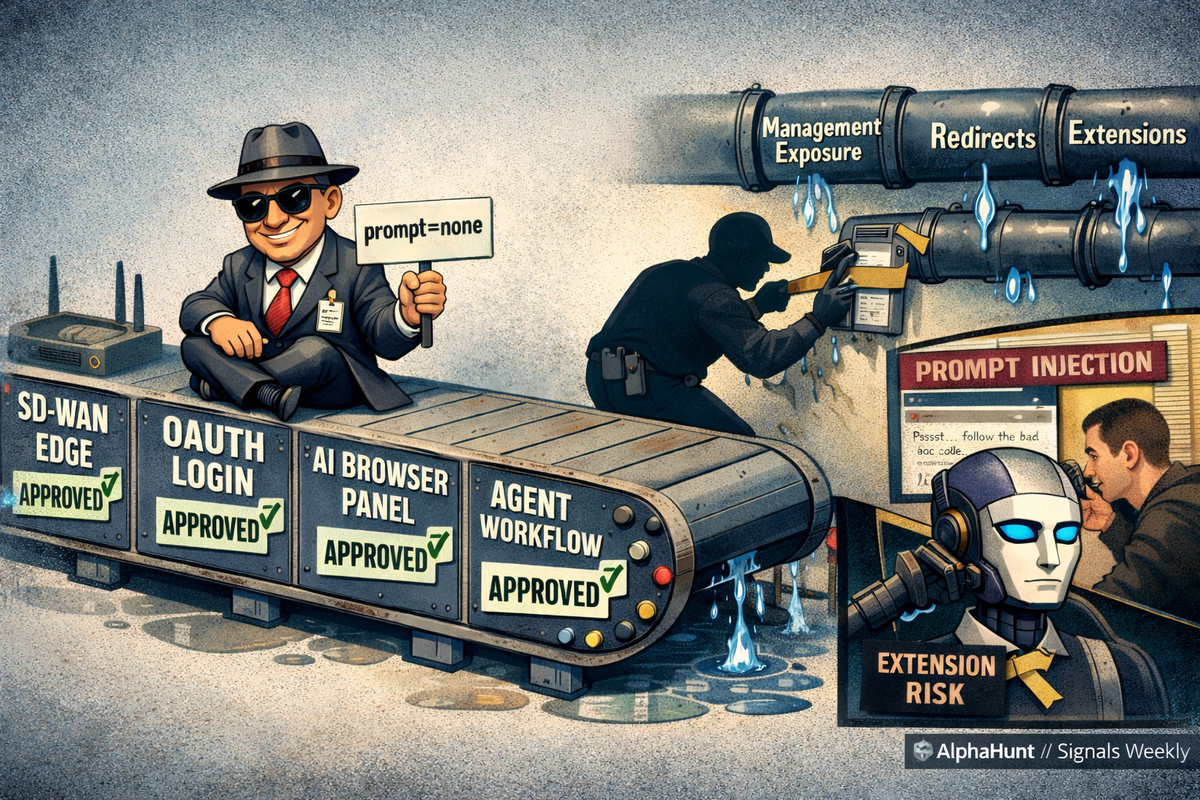
SIGNALS WEEKLY: Cisco Catalyst SD-WAN Exploitation + OAuth Redirect Abuse + Prompt Injection Observed in the Wild
Edge + identity + AI = the new “oops.” 😬🧨🤖 ED 26-03 on Cisco Catalyst SD-WAN exploitation, OAuth redirect abuse that lands users in malware without token theft, plus Gemini panel hijack vs indirect prompt injection in the wild.
TL;DR
- [Vulnerabilities] Active exploitation of Cisco Catalyst SD-WAN (incl. CVE-2026-20127 chained with CVE-2022-20775) has triggered a US Emergency Directive and Five Eyes hunt guidance; prioritize patching, de-internet-exposing management, and hunting for persistence (peering anomalies, version changes, log tampering).
- [Identity & Phishing] Adversaries are abusing OAuth redirection on trusted IdP domains (e.g., login flows with prompt=none and crafted error redirects) to deliver phishing and malware without stealing tokens, requiring enhanced URL, redirect, and download telemetry/detections.
- [AI & Supply Chain] New campaigns target developers via malicious Next.js repos and expose two distinct AI failure modes—browser-extension privilege abuse (e.g., Gemini panel hijack) and web-based indirect prompt injection against agentic workflows—demanding stricter extension governance, CI/CD hardening, and guardrails on AI agents ingesting untrusted web content.
AlphaHunt
Stop doomscrolling, start decisioning. We chewed through the muck so your team doesn’t have to. → Subscribe!
Like this? Forward this to a friend!
(Have feedback? Did something resonate with you? Did something annoy you? Just hit reply! :))
Current Stories
TL;DR
-
[Vulnerabilities] US public-sector and any org running internet-exposed Cisco Catalyst SD-WAN edge/management: Five Eyes and CISA issued ED 26-03 after exploitation of CVE-2026-20127 with CVE-2022-20775; patch, hunt, harden now.
-
[Malware] Enterprises with Ivanti Connect Secure (especially previously remediated incidents): CISA updated RESURGE analysis describing a dormant SSH implant plus network evasion; assume residual compromise and apply CVE-2025-0282 mitigations and IOCs.
-
[Phishing] Microsoft 365/Entra ID tenants and users who regularly authenticate via OAuth flows: Microsoft reports OAuth redirection abuse that routes users from trusted IdP URLs into phishing and malware delivery without token theft; watch prompt=none flows and error redirects.
-
[Geopolitics] US/allied gov, defense industrial base, and critical infrastructure aligned with US-Israel interests: Reporting assesses elevated risk of Iran-aligned activity including DDoS, hack-and-leak, CI targeting, and espionage following Feb 28 strikes.
-
[Incident Response] Healthcare providers and regional hospital networks with limited downtime tolerance: UMMC restored normal clinic operations after a Feb 19 cyberattack, underscoring multi-day recovery realities and the need for resilient offline clinical workflows.
References
-
(2026-02-25) ED 26-03: Mitigate Vulnerabilities in Cisco SD-WAN Systems
-
(2026-02-25) CISA and Partners Release Guidance for Ongoing Global Exploitation of Cisco SD-WAN Systems
-
(2026-02-25) Active exploitation of Cisco Catalyst SD-WAN by UAT-8616
-
(2026-02-26) CISA Issues Updated RESURGE Malware Analysis Highlighting a Stealthy but Active Threat
-
(2026-02-26) MAR-25993211-r1.v2 Ivanti Connect Secure RESURGE
-
(2026-03-02) OAuth redirection abuse enables phishing and malware delivery
-
(2026-03-02) Cyber threat bulletin: Iranian Cyber Threat Response to US Israel strikes, February 2026
-
(2026-03-01) Cyber Advisory: Increased Cyber Risk Amid U.S. Israel Iran Escalation
-
(2026-03-02) This has pulled us together: UMMC prioritizes care, learning during cyberattack
AlphaHunt Converge - Plug in your Flight Crew
Get intelligence where it counts. No dashboards. No detours. AlphaHunt Converge teases out your intent, reviews the results and delivers actionable intel right inside Slack. We turn noise into signal and analysts into force multipliers.
Anticipate, Don’t Chase.


![[SIGNALS WEEKLY] Ransomware’s New Priority Targets—Hypervisors, Recovery Paths, and Control Planes](/content/images/size/w600/2026/03/z-5.png)
![[FORECAST] Will RedNovember be publicly reported to exploit at least one zero-day vulnerability in 2026? Updated 2026-03-24](/content/images/size/w600/2026/03/z-4.png)
![[DEEP RESEARCH] How Malware Uses Solana and EVM Chains to Rotate C2 Without Burning Infrastructure](/content/images/size/w600/2026/03/z-3.png)
![[SIGNALS WEEKLY] GitHub, npm, and Fake Interviews: Why Developer Supply Chain Attacks Are Converging](/content/images/size/w600/2026/03/zz-3.png)