
weekly
SIGNALS WEEKLY: Teams QR/callback phishing beats patching
KEV speedrun of the week 🏁: Office CVE-2026-21509 + WinRAR CVE-2025-8088. Patch anyway… then protect sessions 🍪 (Teams QR/callback lures 📱, SSO/SAML token abuse)

weekly
KEV speedrun of the week 🏁: Office CVE-2026-21509 + WinRAR CVE-2025-8088. Patch anyway… then protect sessions 🍪 (Teams QR/callback lures 📱, SSO/SAML token abuse)

ai
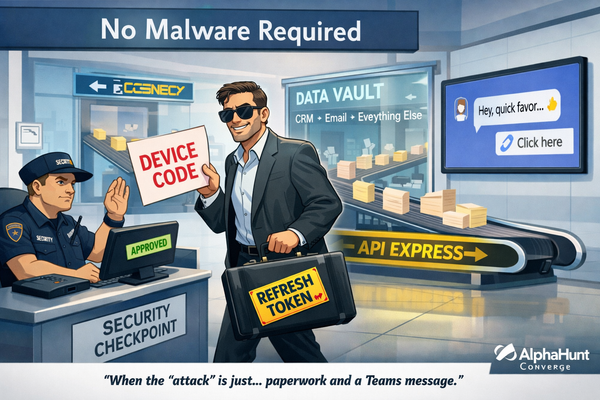
Your “AI coworker” isn’t the breach. The OAuth trust event is. 🔥🕵️♂️ Device-code phishing + consent traps = “approve to exfil.” (And yes, AI agents are already being used as the wrapper.)
identity
No malware. Still owned. 🧾🔑💬 Device-code phishing + Teams as the “lobby” + stolen OAuth tokens = API-speed SaaS exfil. If you’re hunting binaries, you’re late.

weekly
🛫 Your “management plane” is now the battlefield. Cisco Secure Email + HPE OneView are seeing active exploitation, and UAT-8837 is chasing CI targets. Patch like it’s a fire drill. 🔥🧯
![[FORECAST] Integrator CI/CD Compromise by End-2026?](/content/images/size/w600/2026/01/z-6.png)
forecasts
OWASP Top 10:2025 put Software Supply Chain Failures front-and-center. 🧩⚙️ Now the fun question: by end-2026, do we get public root-cause confirmation that an industrial integrator’s CI/CD/build/signing or update channel led to 2+ critical-infra intrusions? 😬

iran
Iran’s internet goes dark → attackers don’t stop. They speed-run creds and hit post-auth collection the moment connectivity blips back. ⏱️🔑👀

weekly
🧭 Taiwan CI pressure looks like recon + access maintenance, not a one-off headline. 🩹 Patch Tuesday + KEV = attacker shopping list. ☁️ And Salesforce Aura/Experience Cloud exposure? No patch… just “surprise, it’s public.”

PIR
Deepfake BEC = the same old fraud… with a way better script. 🎭💸 If payroll/AP changes can happen on “sounds right,” you’re funding someone’s Q1 bonus.
![[FORECAST] CoPhish: The Microsoft Copilot Link That Hands Over Your OAuth Tokens](/content/images/size/w600/2026/01/z-1.png)
forecasts
Will at least one publicly disclosed enterprise breach be confirmed where attackers used a Microsoft Copilot Studio..

weekly
MongoBleed is in KEV: unauth MongoDB memory leak = creds/tokens. Patch + find exposed hosts. Dolby fix + poisoned dev tools too. 🧯🧬👇
![[DEEP RESEARCH] Token Factory: The 5 Costliest US Breaches of 2025](/content/images/size/w600/2026/01/z.png)
breaches
2025’s costliest US breaches: identity, outage math, outcomes Identity-led intrusions at distributors, govtech, healthcare, and an appliance vendor drove nine-figure losses. Outage duration and revocation speed determined the spread between disruption and recovery.
geopolitics
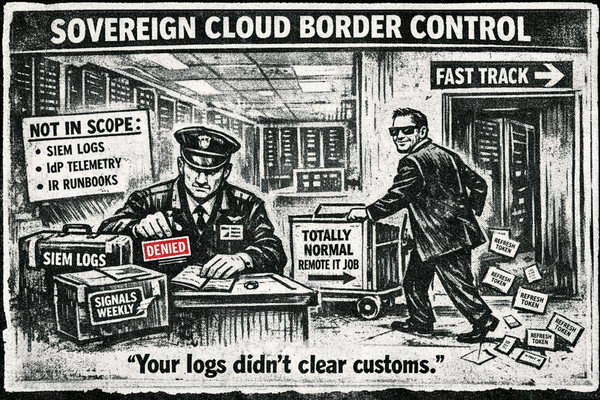
2026 prediction: “sovereign cloud” becomes the #1 way to accidentally create telemetry refugees 🛂☁️ Meanwhile: DPRK “IT workers” in the supply chain + OAuth consent hijacks that laugh at MFA 🔑🎭 What’s your log-clears-customs plan?