The Real Government Fraud Story- Identity Infrastructure
“Fraud” makes it sound random. It isn’t. It’s identity infrastructure with a cash-out layer. Same proofing gaps, same rails, same reusable parts. People keep chasing claims instead of the production line.
Most coverage still treats government fraud like a pile of scams.
That is the wrong frame.
The stronger pattern in recent public case reporting is an organized identity-fraud ecosystem: stolen identities, lightweight document enablement, repeatable enrollment abuse, and faster cash-out. This is less about one fake claim and more about a production line.
That matters because production lines scale. They survive arrests. And they give defenders a better target: stop chasing isolated claims and start breaking the infrastructure that manufactures them.
AlphaHunt
Stop doomscrolling, start decisioning. We chewed through the muck so your team doesn’t have to. → Subscribe!
Like this? Forward this to a friend!
(Have feedback? Did something resonate with you? Did something annoy you? Just hit reply! :))
TL;DR
- The strongest recent public-case signal is identity-enabled fraud against government-funded benefit programs, not just old-school check theft.
- Tax refund and Treasury-check fraud remains a durable second lane with structured laundering behavior.
- Cross-border BEC crews still matter, but the direct recent evidence tying them to government payment workflows is weaker here than for benefits and refunds.
- The bigger issue is reusable infrastructure: identity supply, document enablement, and hybrid cash-out.
- The practical move is to focus less on one bad claim and more on the addresses, phones, devices, documents, and payout rails that keep showing up behind multiple claims.
The key judgment
The most useful way to understand recent fraud affecting government-funded disbursements is not by asking which scam is hottest this week.
It is by recognizing that identity-enabled benefit fraud behaves like an organized service economy.
Recent public case reporting points most clearly to three high-confidence fraud lanes. First, stolen-identity benefit-fraud conspiracies are the clearest and strongest signal. Second, tax refund and Treasury-check fraud remains a proven, repeatable model. Third, cross-border BEC crews remain relevant, but their direct role in government payment fraud is less clearly documented in the recent source set.
The practical point is simple: the center of gravity is moving from isolated fraud events to reusable identity operations. Once you see that, the defensive question changes too. The question is no longer just “How do we stop this claim?” It becomes “What reusable enablers let this ring keep producing claims?”
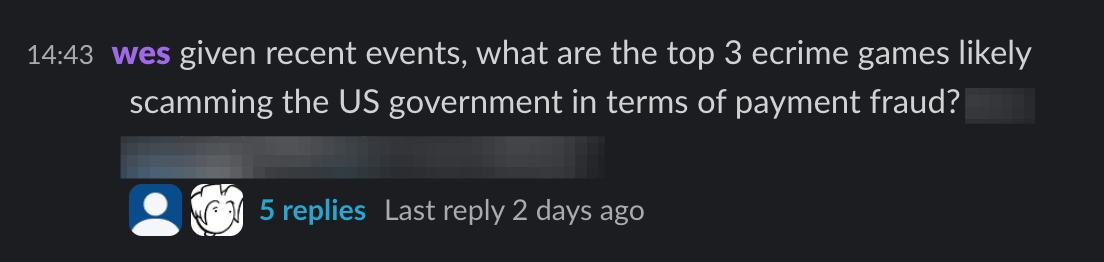
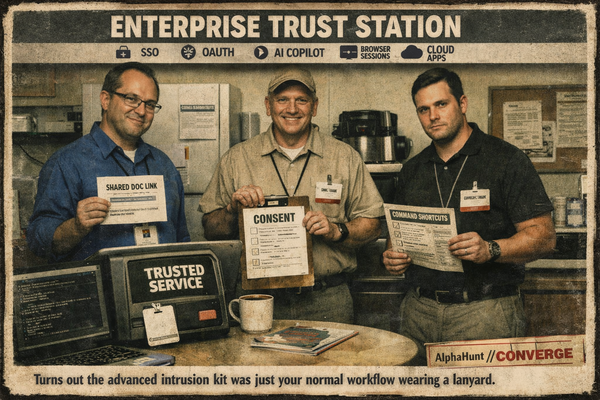
AlphaHunt Converge - Plug in your Flight Crew
Get intelligence where it counts. No dashboards. No detours. AlphaHunt Converge teases out your intent, reviews the results and delivers actionable intel right inside Slack. We turn noise into signal and analysts into force multipliers.
Anticipate, Don’t Chase.
Observed vs. Assessed
Observed
Recent case reporting supports:
- multi-state conspiracies using stolen identities to obtain SNAP, PUA, MassHealth, and Social Security-related benefits
- use of counterfeit identity materials and supporting documents
- prepaid-card, EBT, and fintech-linked cash-out patterns
- tax refund schemes involving Treasury-check issuance and rapid movement of funds
- insider-enabled theft of high-quality PII, including deceased identities
Assessed
Based on those cases, the strongest analytic takeaway is that these fraud schemes behave like an identity infrastructure problem, not just a collection of isolated fraud incidents.
That is an assessment, not a direct quote from the source material.
What changed
Three things stand out.
First, PII sourcing is diversified. Recent case reporting points to bought identity sets, darknet-sold identity artifacts, and insider-enabled theft of cleaner records, including deceased identities. That is a much stronger upstream supply model than the old idea of one breach feeding one fraud ring.
Second, document fraud is operational, not artisanal. These cases are not about perfect fake identities. They are about getting enough proofing to pass the next gate: counterfeit passport images, reused addresses, known phone numbers, and staged credentials that raise assurance just enough to unlock benefits.
Third, cash-out is hybrid. The recent reporting shows EBT abuse, prepaid cards, and fintech transfers like Zelle, Cash App, and Chime. One rail gets pressured, another stays open.
The three strongest visible fraud lanes
1) Stolen-identity fraud against government-funded benefit programs
This is the clearest current signal in recent public reporting.
Recent cases tie organized fraud activity directly to taxpayer-funded or government-administered programs, including multi-state conspiracies involving stolen identity lists, counterfeit identity materials, EBT cards, and prepaid-card-based disbursement.
A precision point matters here: this bucket includes a mix of federal benefits, federally funded but state-administered programs, and state programs. So the best label is not “direct federal payment workflow compromise” in every case. It is broader: government-funded benefit fraud.
2) Tax refund / Treasury-check fraud conspiracies
Still durable. Still structured.
The recent material describes IRS-induced refund issuance, Treasury-check deposits, rapid movement of funds, and the use of business entities and newly opened accounts to create distance from the original payout.
This is the cleanest recent example of direct fraud involving federal tax disbursement mechanics.
3) Cross-border BEC crews
Still dangerous. Just not the clearest direct government-payment signal in this dataset.
These crews remain high-loss actors with disciplined laundering and mule dependencies. But here the overlap with government payment fraud is best treated as an adjacent risk inference, not a fully established conclusion from the recent source set.


![[FORECASTS] From Password Sprays to Tenant Sabotage: The 8-Week Iran Cyber Risk for U.S. and Israeli Orgs - UPDATED: 2026-03-26](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/03/z-6.png)
![[SIGNALS WEEKLY] Ransomware’s New Priority Targets—Hypervisors, Recovery Paths, and Control Planes](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/03/z-5.png)