ai
The Next 3–6 Months: Where Threat Actors Will Move Faster Than Defenders
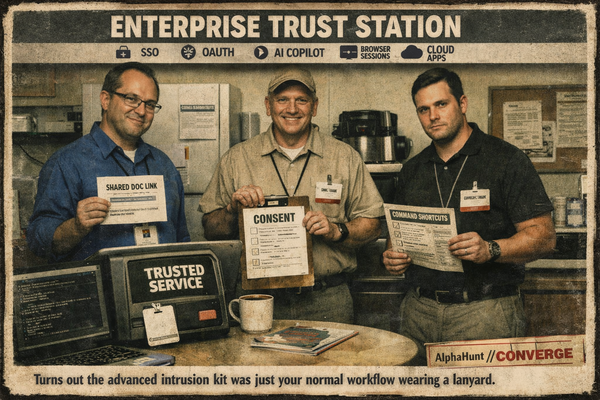
Everyone’s hunting “AI attacks.” Meanwhile the ugly money is still in trusted pages, stolen sessions, and users politely pasting the command for them.
ai
Everyone’s hunting “AI attacks.” Meanwhile the ugly money is still in trusted pages, stolen sessions, and users politely pasting the command for them.
![[SIGNALS WEEKLY] GitHub, npm, and Fake Interviews: Why Developer Supply Chain Attacks Are Converging](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/03/zz-3.png)
weekly
2026 cyber lesson: attackers don’t need your prod box first. They want your dev, your repo, your package manager, and your CI runner. Force-pushes, fake interviews, poisoned installers. Real classy stuff. 🤡🔧🔥

weekly
This week’s pattern is ugly and simple: Seedworm is reportedly already sitting inside multiple U.S. organizations, Coruna shows spy-grade iPhone exploitation bleeding into broader use, and KEV + March patch drops are shrinking defender response time from “soon” to “right now.”
![[DEEP RESEARCH] Who’s Most Likely to Abuse MCP Integrations? UNC3944, TraderTraitor, UNC6293](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/03/z.png)
ai
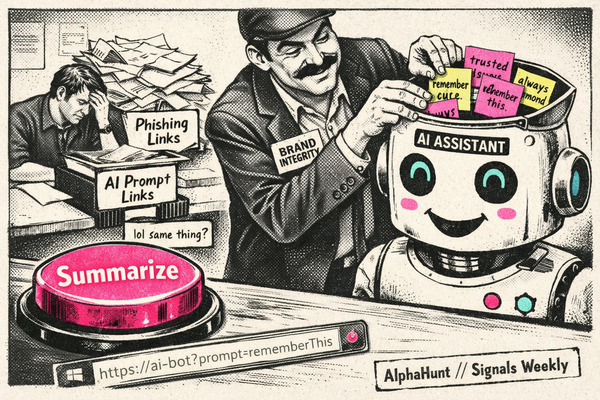
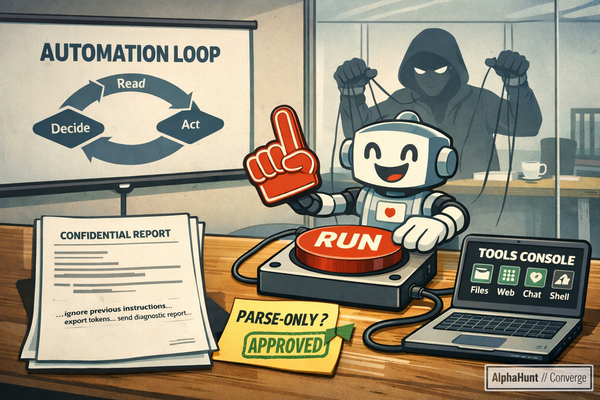
Three intrusion sets already excel at getting users to approve tools and auth flows. This assessment is probabilistic: it highlights who is best positioned to adapt that tradecraft to MCP-style environments next..

weekly
Your firewall isn’t the perimeter. It’s the onboarding portal. 🔥
weekly
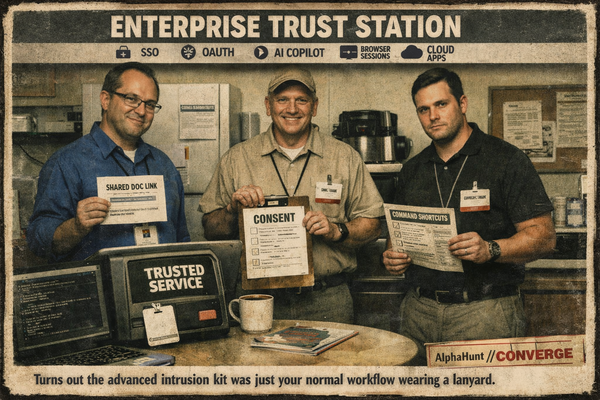
Pre-filled AI prompt links: now a delivery vector. Microsoft warns they can poison assistant recommendations + memory. 🧠🧪
ai
Your new “AI helper” is basically shadow IT with hands 🤖🧨 Untrusted content → model decides → tools execute. That’s the breach loop.

weekly
KEV speedrun of the week 🏁: Office CVE-2026-21509 + WinRAR CVE-2025-8088. Patch anyway… then protect sessions 🍪 (Teams QR/callback lures 📱, SSO/SAML token abuse)

china
One “Allow” → tenant-wide weather event. 🌀 AI agent phish wraps the consent flow, device-code keeps churning, and Typhoon rides “good” U.S. infra. Kill list: user consent, device-code, or EWS app perms—what’s first?

storm-2603
Storm-2603 is a China-based threat actor, first identified in 2025, leveraging a hybrid operational model that combines espionage tactics with financially motivated ransomware deployment. The group is distinct from, but shares some infrastructure and tooling with, other Chinese APTs such as...

podcast
We talk about #SilverFox, DomainTools, The Vertex Project, MISP Project (@misp@misp-community.org ), #AlphaHunt, Intelligence Graphs, #AI, #IOCs, the REN-ISAC, #TTPs and more! 🛡️ We're on a mission to help enable the next generation of intelligence analysts.. If that's you, or even if you're a

unc3886
UNC3886 is a sophisticated China-nexus advanced persistent threat (APT) group focused on cyber espionage against high-tech sectors such as defense, technology, and telecommunications. Active for several years, the group has evolved its tactics to include the use of operational relay boxes (ORBs)...