ai
The Next 3–6 Months: Where Threat Actors Will Move Faster Than Defenders
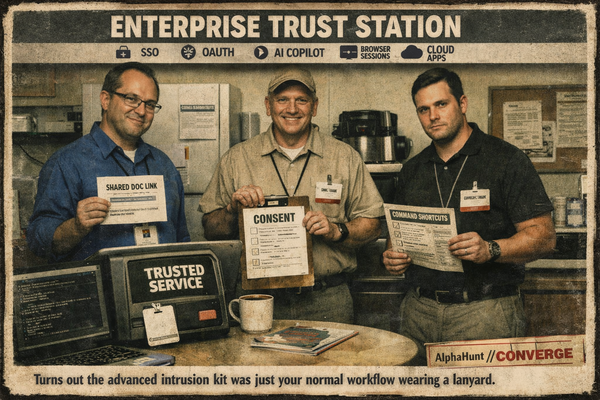
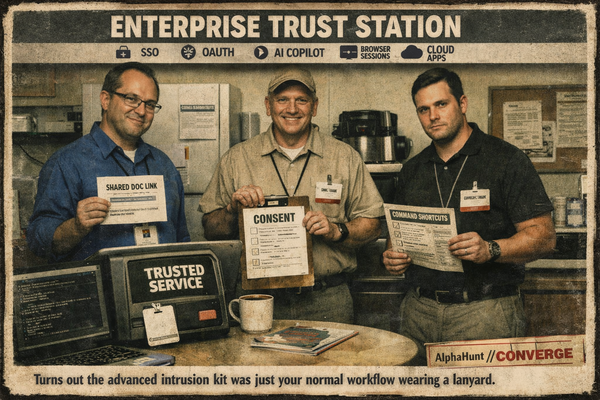
Everyone’s hunting “AI attacks.” Meanwhile the ugly money is still in trusted pages, stolen sessions, and users politely pasting the command for them.
ai
Everyone’s hunting “AI attacks.” Meanwhile the ugly money is still in trusted pages, stolen sessions, and users politely pasting the command for them.
![[FORECASTS] From Password Sprays to Tenant Sabotage: The 8-Week Iran Cyber Risk for U.S. and Israeli Orgs - UPDATED: 2026-03-26](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/03/z-6.png)
forecasts
Iran cyber risk is not about whether they’ll be active. They will. The real question is whether the next 8 weeks produce a publicly attributed, materially disruptive hit with a new twist beyond the usual password-spray sludge. Tenant sabotage is the part to watch. 👀🔥
![[FORECAST] Will RedNovember be publicly reported to exploit at least one zero-day vulnerability in 2026? Updated 2026-03-24](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/03/z-4.png)
forecasts
RedNovember is the kind of crew that turns “it was only an N-day” into a post-incident coping mechanism. We’re at 25% odds they get publicly tied to a true 0-day in 2026. With edge exploitation surging, that’s not exactly comforting. 👀🔥
![[FORECASTS] From Password Sprays to Tenant Sabotage: The 8-Week Iran Cyber Risk for U.S. and Israeli Orgs](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/03/z-2.png)
forecasts
Iran cyber risk isn’t just “watch for wipers.” It’s the same ugly identity-first playbook: password sprays, MFA abuse, cloud access… then maybe admin-plane sabotage. Recent reporting says activity is already reaching U.S. targets. Cute.
![[FORECAST UPDATED] After LockBit and BlackCat, Is Cl0p Really Next in Line?](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/03/zz-1.png)
forecasts
LockBit got Cronos’d. BlackCat caught a DOJ wrench to the teeth. Cl0p is still hanging around the enterprise software aisle like it owns the place. So… is it really next, or are we just recycling takedown fan fiction?
![[FORECAST UPDATED] AI Agents as Regulated C2: Will Anyone Be Forced to Act?](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/02/z-11.png)
forecasts
🤖🔒 AI agents = privileged integrations you can’t see. After GTG-1002 + vendors pushing agent access standards, the next shoe drops: do regulators/hyperscalers force default-on signed connectors + audit logs (aka “regulated C2”)?
![[FORECAST] Fortune 500s: Will Prompt Injection Trick IDE Agent Mode into Running Commands—or Leaking Secrets—by 2026?](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/02/z-10.png)
forecasts
Recent agent-mode rollouts make ‘read files + run tasks’ normal. Prompt injection makes that risky. Here’s the forecast..
![[FORECAST] Dismantled or Displaced? Cambodia’s Scam-Compound Crackdown by 2030?](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/02/z-7.png)
forecasts
Cambodia says it sealed off ~190 scam sites. 🧨 Now the real question: dismantled or displaced? 🧱🚚 Our forecast uses grown-up metrics (convictions + asset denial + independent compound counts).
forecasts
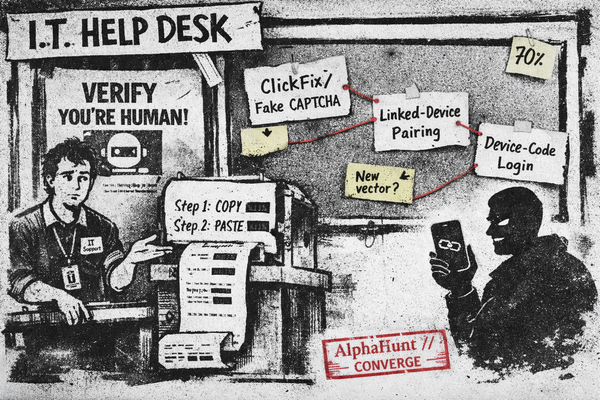
Fake CAPTCHA ➜ “paste this PowerShell.” 🙃 Linked-device pairing ➜ quiet account takeovers. 👻 Device-code phishing ➜ legit login page, attacker gets tokens. 🔑
![[FORECAST] ShinyHunters SaaS Data Theft: Why Non-Ransom Monetization Looks Increasingly Attractive](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/02/z.png)
forecasts
Our new forecast asks: will ShinyHunters make more in 2H 2026 by selling SaaS access/data than by getting paid? Signals say yes. 🕵️♂️💸☁️
![[FORECAST] Integrator CI/CD Compromise by End-2026?](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/01/z-6.png)
forecasts
OWASP Top 10:2025 put Software Supply Chain Failures front-and-center. 🧩⚙️ Now the fun question: by end-2026, do we get public root-cause confirmation that an industrial integrator’s CI/CD/build/signing or update channel led to 2+ critical-infra intrusions? 😬
![[FORECAST] CoPhish: The Microsoft Copilot Link That Hands Over Your OAuth Tokens](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/01/z-1.png)
forecasts
Will at least one publicly disclosed enterprise breach be confirmed where attackers used a Microsoft Copilot Studio..