![[SIGNALS WEEKLY] Tokens, Edges, and Exploits: Shifting Paths to Compromise](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/05/z-9.png)
weekly
[SIGNALS WEEKLY] Tokens, Edges, and Exploits: Shifting Paths to Compromise
The token survived. npm packages, CI/CD runners, and edge boxes keep turning “contained” into “still owned.” The boring weakness became the breach path.
![[SIGNALS WEEKLY] Tokens, Edges, and Exploits: Shifting Paths to Compromise](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/05/z-9.png)
weekly
The token survived. npm packages, CI/CD runners, and edge boxes keep turning “contained” into “still owned.” The boring weakness became the breach path.
![[PODCAST] ANALYST YELLS AT CLOUD](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/05/z-6.png)
podcast
Get closer to the people who understand where threat actors are today — and where they are likely headed tomorrow.
![[GAME THEORY] ShinyHunters- Names Fade. Playbooks Stick.](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/04/zz.png)
gametheory
The ShinyHunters problem isn’t the name. It’s the chain: MFA reset, weird login, OAuth grant, SaaS export, extortion later.
![[RESEARCH] CPU-Z was the lure. The real story is who buys the foothold.](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/04/z-7.png)
vulnerabilities
The scariest part of the CPU-Z mess wasn’t STX RAT. It was the customer profile. Trusted utility, power-user endpoint, resale-ready access. Same old crime economy, better packaging.
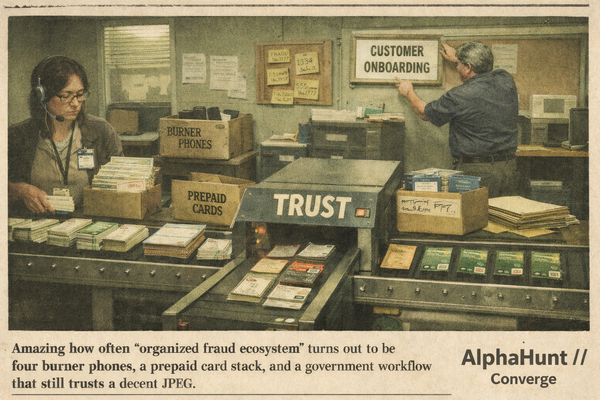
fraud
“Fraud” makes it sound random. It isn’t. It’s identity infrastructure with a cash-out layer. Same proofing gaps, same rails, same reusable parts. People keep chasing claims instead of the production line.
![[SIGNALS WEEKLY] GitHub, npm, and Fake Interviews: Why Developer Supply Chain Attacks Are Converging](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/03/zz-3.png)
weekly
2026 cyber lesson: attackers don’t need your prod box first. They want your dev, your repo, your package manager, and your CI runner. Force-pushes, fake interviews, poisoned installers. Real classy stuff. 🤡🔧🔥
![[FORECASTS] From Password Sprays to Tenant Sabotage: The 8-Week Iran Cyber Risk for U.S. and Israeli Orgs](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/03/z-2.png)
forecasts
Iran cyber risk isn’t just “watch for wipers.” It’s the same ugly identity-first playbook: password sprays, MFA abuse, cloud access… then maybe admin-plane sabotage. Recent reporting says activity is already reaching U.S. targets. Cute.
![[FORECAST] Dismantled or Displaced? Cambodia’s Scam-Compound Crackdown by 2030?](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/02/z-7.png)
forecasts
Cambodia says it sealed off ~190 scam sites. 🧨 Now the real question: dismantled or displaced? 🧱🚚 Our forecast uses grown-up metrics (convictions + asset denial + independent compound counts).

weekly
🧭 Taiwan CI pressure looks like recon + access maintenance, not a one-off headline. 🩹 Patch Tuesday + KEV = attacker shopping list. ☁️ And Salesforce Aura/Experience Cloud exposure? No patch… just “surprise, it’s public.”

scam
Holiday scammers are running peak-season ops 📦🎄 “Delivery problem” texts, AI “family emergency” calls, and “pay via gift card/Zelle” pressure. Rule: don’t click, hang up + call back, never gift cards/crypto/wires.

forecasts
We’re at 29% that RedNovember will be publicly reported exploiting at least one zero‑day in 2026 under strict timing and attribution rules. The hinge is whether the group escalates beyond PoC‑driven N‑day edge exploits and whether attribution survives rebranding.

romance-scam
Thailand pulled the plug. The grift brought generators + Starlink. Shift north→south (Shwe Kokko/Myawaddy; Tachileik/Mae Sai). Squeeze OTC cash-outs + first-funding friction, or watch it respawn.