[FORECASTS] From Password Sprays to Tenant Sabotage: The 8-Week Iran Cyber Risk for U.S. and Israeli Orgs
Iran cyber risk isn’t just “watch for wipers.” It’s the same ugly identity-first playbook: password sprays, MFA abuse, cloud access… then maybe admin-plane sabotage. Recent reporting says activity is already reaching U.S. targets. Cute.
![[FORECASTS] From Password Sprays to Tenant Sabotage: The 8-Week Iran Cyber Risk for U.S. and Israeli Orgs](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w1200/2026/03/z-2.png)
TL;DR
Question
Will Iran-linked cyber operators (state units and aligned proxy/hacktivist ecosystem) conduct ≥1 novel, materially disruptive or data-compromising cyberattack against U.S. or Israeli organizations in the next 8 weeks, attributable with high confidence by credible authorities?
Executive Forecast
61% means a novel, confirmed, threshold-crossing Iran-linked incident against U.S./Israeli orgs is more likely than not in the next 8 weeks, but far from certain. The most likely “novelty” is how identity compromise is converted into impact (admin-plane/tenant sabotage) rather than a brand-new strategic objective. Watch for early signs in M365/Azure/Okta authentication + MFA/device registration events, and for escalation from access into policy and admin control changes.
AlphaHunt
Stop doomscrolling, start decisioning. We chewed through the muck so your team doesn’t have to. → Subscribe!
Like this? Forward this to a friend!
(Have feedback? Did something resonate with you? Did something annoy you? Just hit reply! :))
Forecast Card
-
Question: Will Iran-linked cyber operators (state units and aligned proxy/hacktivist ecosystem) conduct ≥1 novel, materially disruptive or data-compromising cyberattack against U.S. or Israeli organizations in the next 8 weeks, attributable with high confidence by credible authorities?
-
Resolution Criteria: Yes if, between now and the horizon date, there is at least one incident meeting all of the following:
(1) Attribution quality (required): Public, credible confirmation of Iran nexus by any of: victim disclosure, U.S. or Israeli government statement/advisory, UK NCSC statement, or consensus top-tier vendor reporting with evidence. Hacktivist Telegram claims alone do not count.
(2) Material impact (must meet ≥1):
- IT disruption: ≥ 500 endpoints impacted OR ≥ 5% of endpoints in the org (whichever is smaller) rendered unusable/encrypted/wiped OR ≥ 50 servers affected; OR
- Service outage: a critical business/public service outage of ≥ 8 hours (for internal-only systems: ≥24 hours); OR
- OT/ICS service effect: confirmed degradation/interrupt of a physical process impacting ≥ 10,000 customers/users OR any safety-critical operational shutdown attributable to cyber; OR
- Data compromise: confirmed exfiltration of ≥ 10 GB of sensitive org data OR ≥ 100,000 individuals’ records OR any regulated sensitive class at scale (e.g., health records, national IDs), confirmed by the victim/regulator/forensics.
(3) Novelty checklist (must meet ≥1 “new” dimension vs. the last ~12 months of commonly documented Iran tradecraft in major government advisories):
- New initial access class: e.g., helpdesk-targeted deepfake/voice vishing for MFA reset, mobile app–delivered spyware at scale, or supply-chain compromise of a widely used SaaS/MSP tool affecting downstream victims; OR
- New impact mechanism: e.g., destructive action via cloud/device management plane (MDM/RMM/IdP admin policy abuse) rather than malware-on-host; OR
- New target class: a sustained Iran-linked campaign causing material impact in a previously lower-frequency class for Iran during escalations (e.g., U.S. emergency alerting ecosystems, municipal public safety dispatch, Israel-adjacent diaspora institutions outside Israel); OR
- New toolchain: a newly documented wiper/backdoor/mobile implant family or a clearly novel variant acknowledged by authorities/vendors as new in this wave.
No if there is no such confirmed incident meeting the thresholds above (routine DDoS/defacement, recycled leaks, or unverified hacktivist claims do not qualify).
-
Horizon: 2026-05-11 23:59 America/New_York (8 weeks)
-
Probability (Now): 61% | Log-odds: 0.45
-
Confidence in Inputs: Medium (improved auditability; still uncertainty on “novelty” emergence timing)
-
Base Rate: 30% from reference class: “8‑week windows during elevated Iran–Israel / Iran–U.S. tensions yield frequent attempts and some confirmed compromises, but novel + material outcomes are materially less common than DDoS/credential campaigns.”
Audit note: Base rate anchored to (a) recurring Iran-linked CI credential/access activity described in joint government advisories and (b) historical “significant incident” frequency summaries (CSIS) rather than any single vendor report.
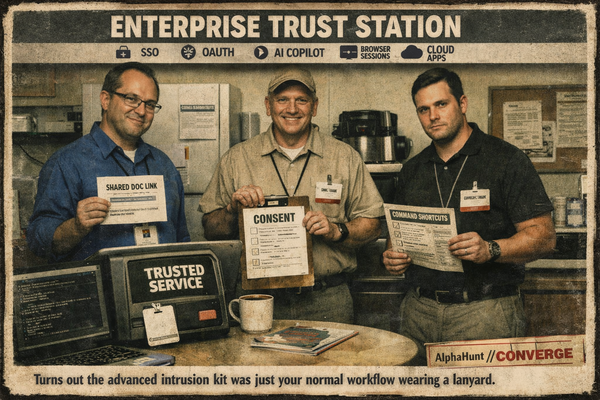
AlphaHunt Converge - Plug in your Flight Crew
Get intelligence where it counts. No dashboards. No detours. AlphaHunt Converge teases out your intent, reviews the results and delivers actionable intel right inside Slack. We turn noise into signal and analysts into force multipliers.
Anticipate, Don’t Chase.


![[FORECASTS] From Password Sprays to Tenant Sabotage: The 8-Week Iran Cyber Risk for U.S. and Israeli Orgs - UPDATED: 2026-03-26](https://storage.ghost.io/c/06/e5/06e5730b-7d78-4713-9cec-6cba31d297f5/content/images/size/w600/2026/03/z-6.png)